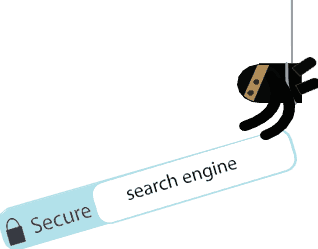
The Top Browser Threats When end users venture out onto the Internet, it’s easy to get tangled up in the vast web of threats lurking on many website pages. Some of them are readily apparent, but others are well hidden. Malvertising—a form of malicious code that distributes malware through online advertising—can be hidden within […]